Using an Aladdin eToken PRO to store grid certificates
A very secure way to store grid certificates is on an Aladdin eToken (http://www.aladdin.com/eToken/default.asp). These tokens are so-called smartcards with a USB form factor. They can be used to securely generate and store X509 certificates and/or SSH keys. The public part of an X509 certificate can be accessed by an application, but the corresponding private key can never be copied off an eToken. This, in theory, makes such a device ideal for storing sensitive data such as grid certificates.
Platform support
With some tinkering it is possible to use an eToken on
- Windows
- Linux:
- Redhat Enterprise Linux 4 and compatible (Scientific Linux 4, CentOS 4)
- Fedora Core 4 or higher
- Suse 10 or higher
- MacOS X
This document tries to explain the tinkering ...
Note that not all functions are available on all platforms. Currently , it is not possible to reformat an eToken on Linux. This can only be done on Windows (and perhaps MacOS, but this is untested).
Downloading the Aladdin eToken RTE software
Due to licensing restrictions we cannot supply the eToken drivers and libraries on this site, these need to be downloaded from Aladdin. You can find the required software on the web:
- Windows: http://www.aladdin.ru/bitrix/redirect.php?event1=download&goto=/upload/iblock/2c0/RTE_3.65.zip
- Linux: http://www.aladdin.ru/bitrix/redirect.php?event1=download&goto=/upload/iblock/179/eToken_PKI_Client_for_Linux_v3_65.rar
- MacOS: http://www.aladdin.ru/bitrix/redirect.php?event1=download&goto=/upload/iblock/973/PKI_3_65_Mac.zip
(the files on Aladdin's Russian site do not require a password to unpack them, the ones on the US site do...)
To unpack the Linux archive, the rar command is required.
Important
As of yet, do NOT install the PKI Client 4.0 software (Windows only)! eTokens initialized with this version of the Aladdin software are completely unusable by older releases. If you want to use your eToken on any other platform than Windows then stick with the RTE_3.65 software release instead.
Installing the Aladdin eToken RTE software
Windows
Unzip the RTE_3.65.zip archive and install RTE_3.65.msi file. After rebooting the operating system should recognize the eToken automatically when it is inserted (a red light will start to glow inside the eToken).
You can now continue on to Testing the eToken RTE software.
Linux
Prerequisites
Before running the installation script, verify that the PC/SC Lite pcscd deamon is installed on your box. The eToken installation script is very picky about the location where this deamon is installed and will refuse to continue if it is not present in
/usr/local/sbin/pcscd
If your pcscd deamon is installed elsewhere then create a symlink.
RHEL4 Pre-installation
The Mkproxy.tar.gz tarball contains all the required binaries for RHEL4 compatible platforms. After unpacking the tarball, copy over the files to their respective locations:
cd ./rhel4 cp -rp bin/* /usr/local/bin cp -rp lib/* /usr/local/lib cp -rp sbin/* /usr/local/sbin
Running the Aladdin installation script
Unpack the .rar file using
rar x eToken_PKI_Client_for_Linux_v3_65.rar
which will extract the files
- etoken-3-65.3-linux-Fedora-i386.tar.gz : Fedora Core 4 and higher
- etoken-3-65.3-linux-redhat-i386.tar.gz : Redhat Enterprise Linux 4 and higher
- etoken-3-65.3-linux-suse-i386.tar.gz : Novell Suse Linux
(and a few others) to the current directory.
Extract the .tar.gz tarball that closest matches your Linux distribution. All files will be extracted to a directory etoken-3-65.3-linux-i386. cd into this directory and run the installation program:
./petoken install 4
where the number 4 indicates how many tokens you wish to support simultaneously (this is the default value).
./petoken install 4 Starting Aladdin eTokend daemon: Starting pcscd daemon: Modifying /etc/ld.so.conf Aladdin Etoken RTE installation finished Warning: you have two pcscd installations (in /usr and in /usr/local)
Installation is complete. The installation script will have installed the appropriate deamons and /etc/init.d startup script, such that the eToken software is loaded at system startup. For more details, see Linux eToken daemons.
The petoken installation script is a total nightmare. If anything goes wrong during installation then the installation is aborted. You will need to run
./petoken uninstall
before you can continue. However , the 'uninstall' command also erases the installation program itself, so you need to unpack the .tar.gz tarball again before you can continue.
Post-installation cleanup
If you have installed the Aladdin RTE software on a Linux system which uses udev to provide hotplugging device support - i.e. Fedora Core 5 or any system running Linux kernel 2.6.16 or higher - then you need to do a post-installation cleanup. If this step is skipped your eToken will not be accessible after the next reboot.
1. install this version of etoken.conf in /etc/reader.conf.d:
# Aladdin eToken virtual reader #0 FRIENDLYNAME "AKS ifdh" DEVICENAME /dev/null LIBPATH /usr/local/lib/aksifdh.so CHANNELID 0x11111111 # Aladdin eToken virtual reader #1 FRIENDLYNAME "AKS ifdh" DEVICENAME /dev/null LIBPATH /usr/local/lib/aksifdh.so CHANNELID 0x11111112 # Aladdin eToken virtual reader #2 FRIENDLYNAME "AKS ifdh" DEVICENAME /dev/null LIBPATH /usr/local/lib/aksifdh.so CHANNELID 0x11111113 # Aladdin eToken virtual reader #3 FRIENDLYNAME "AKS ifdh" DEVICENAME /dev/null LIBPATH /usr/local/lib/aksifdh.so CHANNELID 0x11111114
2. install these 20-etoken.rules in /etc/udev/rules.d:
ACTION=="add", SUBSYSTEM=="usb_device", \
SYSFS{idVendor}=="0529", SYSFS{idProduct}=="0600", SYSFS{product}=="Token 4.2*", \
RUN="/etc/hotplug.d/usb/etoken.hotplug"
3. install this version of the etoken.hotplug script in /etc/hotplug.d/usb:
#!/usr/bin/perl
use Socket;
#use Data::Dumper;
open STDERR, ">> /var/log/etoken.log";
#print STDERR Dumper(\%ENV);
# check environment
die "Call with undefined environment is ignored" unless defined($ENV{"DEVNAME"}) && defined($ENV{"ACTION"});
$device = $ENV{"DEVNAME"};
# build request structure for insertion/removal
$data_len = length($device) + 1; # one more for null-terminator
$magic = 0x55AAAA55;
$insert_token = 1;
$remove_token = 2;
$command = ($ENV{ACTION} eq "add") ? $insert_token : $remove_token;
$data = pack("IIIIIIa" . $data_len, $magic, 0, 0, $command, $data_len, 0, $device);
$socket_name = "/var/tmp/.etokend";
# open socket with eTokend
socket (SOCK,PF_UNIX,SOCK_STREAM, 0) or die "socket: $!";
connect (SOCK, sockaddr_un($socket_name)) or die "connect $socket_name: $!";
print SOCK $data;
close SOCK;
MacOS
Details not yet known.
Testing the eToken RTE software
Windows
You can access your eToken using the software installed by the RTE_3.65.msi installation package (usually in Start->Programs->eToken).
If you have installed Cygwin ( http://www.cygwin.com/ ) and the Mkproxy.tar.gz tarball you can also access your eToken using the pkcs11-tool command:
- start a Cygwin shell
- go to the directory where you have unpacked the Mkproxy.tar.gz tarball
- type
cd cygwin/bin ./pkcs11-tool --module=$WINDIR\\system32\\etpkcs11.dll -L
to list all inserted tokens (mind the double back-slashes!)
Note This works only if you are logged in locally on the Windows machine. This will not work when logging in remotely using either a Cygwin sshd service or Remote Desktop.
Linux
If you have installed either the opensc toolkit or the the Mkproxy.tar.gz tarball you can access your eToken using the pkcs11-tool command:
- go to the directory where you have unpacked the Mkproxy.tar.gz tarball
- type
export PATH=$PATH:<platform>/bin
- then type
pkcs11-tool --module=/usr/local/lib/libetpkcs11.so -L
which should return
Available slots: Slot 0 AKS ifdh 00 00 token state: uninitialized Slot 1 (empty) Slot 2 (empty) Slot 3 (empty)
Congratulations, your eToken is ready for use!
Linux eToken daemons
On Linux, the eToken RTE installation scripts sets up 3 daemons
- /etc/rcN.d/S10etoken -> ../init.d/etokend
- /etc/rcN.d/S20etoken -> ../init.d/pcscd
- /etc/rcN.d/S30etoken -> ../init.d/etsrvd
(Nice naming convention, eh?)
where N is the runlevel at which the daemons are started (usually 2345).
The first deamon, etokend, is the low level daemon which talks to the eToken itself.
The second deamon, pcscd, is the PC/SC card service. Unfortunately, the eToken installer overwrites any existing pcscd scripts. If you want, you can safely restore the pcscd script from your favorite Linux distribution. However, it is important that this daemon is started after the etokend daemon is started.
The etsrvd daemon is started last. It is not strictly required to access your eToken, but it does speed up access by a factor of 2 or more. Sometimes this daemon does not seem to start at system boot-up, however. A manual (re)start of the daemon usually fixes this.
Why not use the OpenSC tools?
The OpenSC project ( http://www.opensc.org ) also provides driver software for Aladdin eTokens. However, the OpenSC software stack only supports eTokens running Siemens CardOS M4. Our eTokens use a newer version of the Siemens CardOS:
# lsusb -v -d 0529:0600 | grep iProduct iProduct 2 Token 4.25.1.2 2.6.189
This means that this eToken is running CardOS 4.25.1.2, which is not supported by OpenSC. Even the latest development version of OpenSC (cvs HEAD branch) , which claims support for CardOS 4.2+, cannot successfully connect to these eTokens.
Initializing your eToken (Windows only)
Note' Currently you can only initialize your eToken on the Windows platform. It will not work on Linux. This is most likely due to missing functionality in the Linux Aladdin RTE software.
To initialize your eToken for the first time you can use either the Windows client software (Start->Programs->eToken->eToken Properties) or you can use pkcs11-tool :
# pkcs11-tool --module $WINDIR\\system32\\etpkcs11.dll --init-token --label "Your Label" --so-pin Your_New_SO_PIN
where Your_New_SO_PIN is the new Security Officer Password. You will be prompted for the existing SOPIN (through a pop window). The default value for the SOPIN is '1234567890' After typing in the correct (old) SOPIN you will see a message like this:
Token successfully initialized
You can now use
pkcs11-tool ---module $WINDIR\\system32\\etpkcs11.dll -L
to view the status of your eToken:
Available slots: Slot 0 AKS ifdh 00 00 token state: uninitialized Slot 1 (empty)
As you can see it remains in the status "uninitialized" but it is ready for use.
Initializing your user PIN
After initializing or reformatting your eToken you must initialize the user password ('pin') before you can store any data on it. Initializing the user pin can be done on both Windows and Linux.
Note
On Windows
PKCS11_MOD=$WINDIR\\system32\\etpkcs11.dll
On Linux
PKCS11_MOD=/usr/local/lib/libetpkcs11.so
# pkcs11-tool --module $PKCS11_MOD --init-pin Please enter SO PIN: Please enter the new PIN: Please enter the new PIN again: User PIN successfully initialized
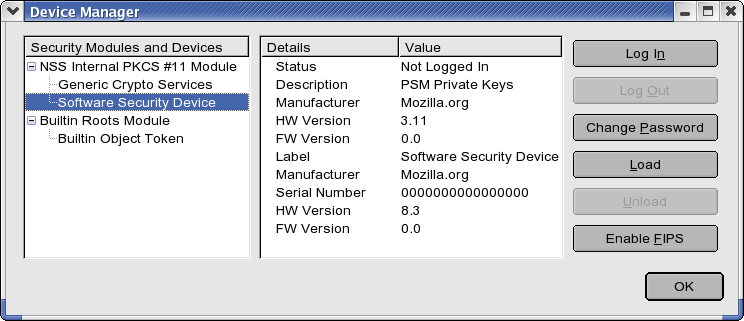
Using your eToken in Firefox
A very easy method for importing (or removing) keys in your eToken is to add the eToken as a Security Device in Firefox. To add your eToken as a security device , follow these steps
- Start Firefox
- (Linux) Go to Edit->Preferences->Advanced->Tab "Encryption"
- (Windows) Go to Tools->Options->Advanced->Tab "Encryption"
- Click on 'Security Devices'
You should see a screen similar to
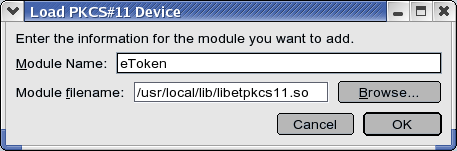
- Click on 'Load'
- In the next screen, enter a (possibly useful) name for this module and Click on 'Browse' to select the appropriate PKCS11 module
- (Linux) choose /usr/local/lib/libetpkcs11.so
- (Windows) choose %WINDIR%\\system32\\etpkcs11.dll
- Click 'OK'
You are now ready to use your eToken as a PKCS11 device within Firefox and can import your existing X509 grid certificate (in PKCS12 format!) into your browser. Make sure that you select the eToken as the security device where you want to store the grid certificate.
A similar procedure applies to Thunderbird, so that you can use an X509 certificate from your eToken to digitally sign your email messages with. In Thunderbird 1.5 , a similar screen can be found under Edit->Preferences->Privacy->Tab "Security".
Generating or storing a grid certificate on the eToken
Now that you have initialized you can either generate a new certificate/private key pair on the eToken itself (very secure!) or you can load your existing grid certificate onto the eToken. This is explained in Storing your grid certificate on an Aladdin eToken.
Generating grid proxies using an eToken
It is also possible to generate a grid proxy using the eToken. This is explained in Using an Aladdin eToken PRO to generate grid proxies.